Harvest Now, Decrypt Later: The Attack Already Happening
Encrypted data is being stolen today for quantum decryption tomorrow. Intelligence agencies warn your secrets may already be compromised — here's what's at stake.
Intelligence agencies are collecting encrypted internet traffic today — not because they can read it, but because they're betting they'll be able to in 10 years. Your data is already in their archive. This isn't speculation from paranoid security researchers; it's the explicit operating doctrine of state-level actors including China's Ministry of State Security and Russia's SVR, documented in classified assessments that have trickled into public awareness through intelligence leaks and official warnings.
According to a 2022 NSA memorandum, the "Harvest Now, Decrypt Later" (HNDL) threat represents one of the most significant long-term risks to national security infrastructure. The math is brutal: RSA-2048 encryption, which protects roughly 90% of HTTPS connections globally, would require approximately 4,000 logical qubits to break using Shor's algorithm. IBM's current quantum processor, Condor, stands at 1,121 physical qubits — but physical qubits aren't logical qubits. With error correction overhead, we're looking at a gap that could close within 8-15 years, according to the Quantum Economic Development Consortium's 2023 roadmap.
The question isn't whether your encrypted communications are being harvested. The question is: what happens when the vault finally opens?
How the Attack Works: A Quantum Time Machine
To understand why HNDL is so insidious, we need to examine the asymmetric relationship between current encryption standards and quantum computational theory.
The Mathematics of Inevitable Collapse
Modern public-key cryptography rests on mathematical problems that are computationally hard for classical computers but trivial for quantum ones. RSA encryption, for instance, derives its security from the difficulty of factoring large semiprimes. For a 2048-bit key, classical factorization would require approximately:
$$T_{classical} \approx \frac{e^{(\ln N \cdot \ln\ln N)^{1/3}}}{(\ln N)^{2/3}}$$
This translates to roughly 300 trillion years on current hardware. However, Shor's algorithm running on a sufficiently powerful quantum computer reduces this to:
$$T_{quantum} = O((\log N)^3)$$
In practical terms: hours or days, not trillions of years.
[!INSIGHT] The cryptographic assumptions underlying global e-commerce, diplomatic communications, and military planning assume a computational barrier that quantum mechanics fundamentally dissolves. We've built our digital civilization on a foundation with an expiration date we refused to acknowledge.
What's Actually Being Harvested?
Intelligence assessments suggest state actors are targeting several categories of high-value encrypted data:
1. Diplomatic Communications: State Department cables, foreign ministry communications, and encrypted diplomatic channels carry classification durations of 25-50 years. A diplomatic secret from 2024 remains strategically valuable in 2040.
2. Military and Intelligence Data: Weapons system specifications, intelligence asset identities, and strategic planning documents often have extended classification periods. The Pentagon's 2023 Quantum Vulnerability Assessment identified over 47 classified programs whose compromise would constitute "exceptionally grave damage" to national security.
3. Intellectual Property: Trade secrets, proprietary research, and pre-patent filings. Chinese cyber operations, particularly APT41, have been documented exfiltrating encrypted research data from pharmaceutical companies and semiconductor manufacturers.
4. Personal Identity Information: Biometric data, social security numbers, and medical records enable long-term identity compromise. A 25-year-old's medical records stolen today could enable blackmail in 2045.
“"We assess with high confidence that nation-state adversaries are conducting long-term operations to acquire and store encrypted data with the expectation that advances in quantum computing will eventually enable decryption. This threat is not theoretical”
The Adversaries: Documented Operations
China's Strategic Infrastructure Collection
The People's Republic of China has been the most aggressive practitioner of HNDL operations. In 2023, the Five Eyes intelligence alliance (US, UK, Canada, Australia, New Zealand) issued a joint advisory identifying Chinese state-sponsored actors as the primary threat actors in quantum-relevant data exfiltration.
The Volt Typhoon incident, disclosed in May 2023, revealed that Chinese hackers had maintained access to critical infrastructure networks — including telecommunications and energy sectors — for an estimated five years. While the immediate concern was pre-positioning for disruptive attacks, security analysts noted the access would have enabled wholesale traffic capture.
A particularly revealing case: Microsoft's 2023 Digital Defense Report documented Chinese acquisition of encrypted traffic from underwater cable landing stations. These facilities, where trans-oceanic cables connect to terrestrial networks, represent chokepoints where bulk collection is technically feasible.
Russia's Historical Precedent
Russia's FSB operates System for Operative Investigative Activities (SORM), which legally mandates that telecommunications providers install equipment enabling state access to communications. While SORM's classical use involves real-time surveillance with legal process, intelligence analysts believe encrypted traffic captured through SORM infrastructure is archived for future analysis.
The 2016 Shadow Brokers leak, which disclosed NSA hacking tools, also contained references to internal NSA concerns about Russian quantum computing investments. One classified presentation, dated 2015, noted: "Russian Federation quantum research funding has increased 400% since 2010, with explicit statements from Kremlin officials about cryptographic applications."
[!NOTE] North Korea and Iran lack sophisticated quantum research programs but benefit from Russian and Chinese technology transfers. Intelligence assessments suggest both nations receive quantum-decrypted intelligence from their patrons, creating a secondary proliferation risk.
The Timeline: When Does the Vault Open?
Predicting when quantum computers will break current encryption is notoriously difficult, but several frameworks help bound the problem.
The Logical Qubit Challenge
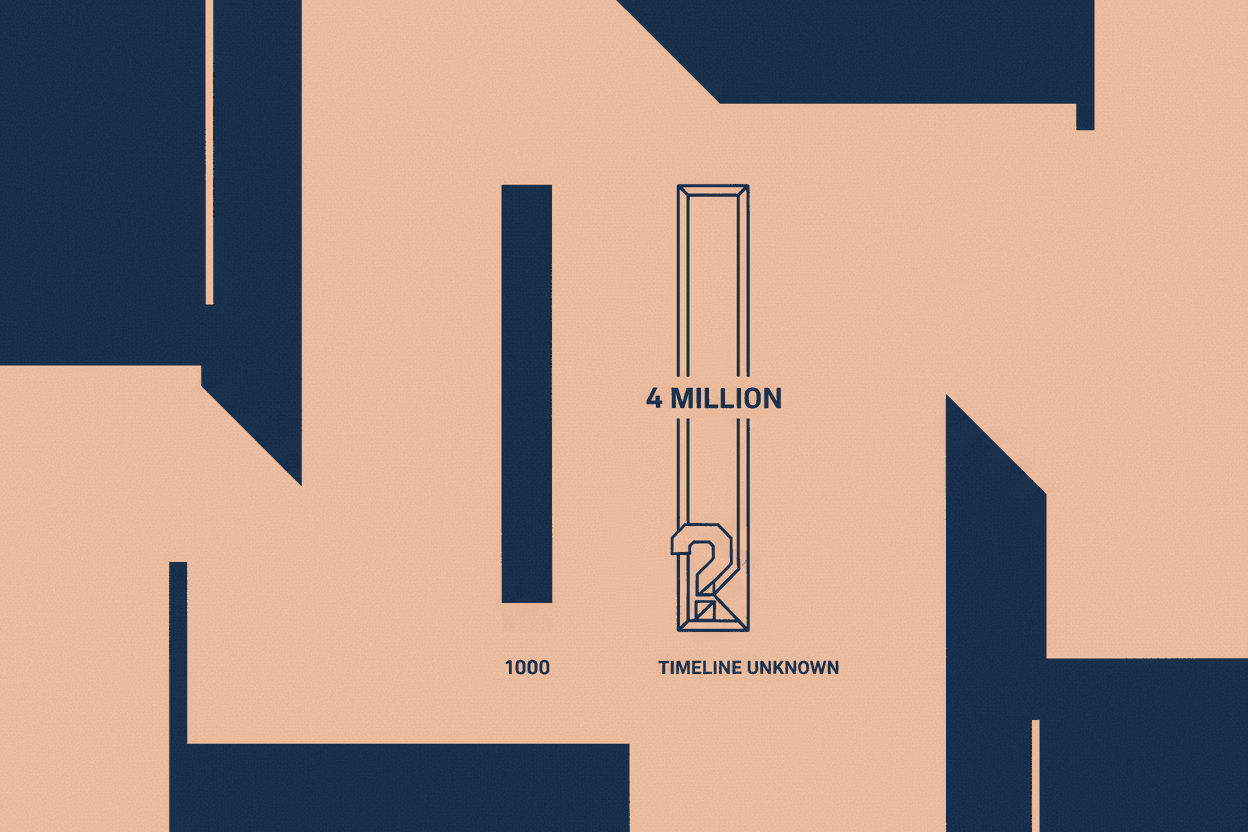
Physical qubits are error-prone. To perform reliable computations, physical qubits must be organized into error-corrected logical qubits. Current estimates suggest a ratio of 1,000 to 10,000 physical qubits per logical qubit, depending on the error correction scheme.
To break RSA-2048:
- Required logical qubits: ~4,000
- Required physical qubits (conservative): 4 million to 40 million
IBM's 2023 Condor processor has 1,121 physical qubits. Their 2025 roadmap targets 100,000+ physical qubits. Even accounting for aggressive scaling, cryptographically relevant quantum computers (CRQCs) are unlikely before 2030.
However, a 2023 National Academies report identified a concerning possibility: unexpected algorithmic breakthroughs could accelerate timelines dramatically. Just as deep learning progressed far faster than AI researchers predicted, quantum algorithm efficiency could improve non-linearly.
The Mosca Inequality
Michele Mosca, co-founder of the Institute for Quantum Computing at the University of Waterloo, formulated a now-famous inequality for cryptographic risk assessment:
$$X + Y > Z$$
Where:
- X = Time to transition to quantum-safe infrastructure
- Y = Time data must remain secure
- Z = Time to build a CRQC
If $X + Y > Z$, your data is at risk. For most organizations, X (transition time) is 5-10 years. Y (security lifetime) ranges from a few days to 50+ years. If Z is 15 years, data requiring 20 years of security that hasn't started transitioning is already compromised.
[!INSIGHT] The Mosca Inequality reveals a terrifying truth: even if quantum computers won't arrive for 20 years, data with 25-year security requirements is already vulnerable if we haven't begun transitioning. The attack hasn't just started — for some secrets, it may already be too late.
The Defense: Post-Quantum Cryptography
NIST's Race Against Time
In 2016, the National Institute of Standards and Technology launched the Post-Quantum Cryptography Standardization Project — an open competition to identify quantum-resistant algorithms. After six years and four elimination rounds, NIST announced its initial selections in 2022:
Primary Algorithms:
- CRYSTALS-Kyber (key establishment): Based on the Learning With Errors problem over module lattices
- CRYSTALS-Dilithium (digital signatures): Also lattice-based, with rigorous security proofs
Backup Algorithms:
- FALCON (signatures): Uses NTRU lattices, more compact than Dilithium
- SPHINCS+ (signatures): Hash-based, providing defense-in-depth against lattice vulnerabilities
The mathematical foundation differs fundamentally from RSA and elliptic curve cryptography. Lattice problems, even for quantum computers, currently have no known sub-exponential solutions. Shor's algorithm doesn't apply; Grover's search provides only quadratic speedup, which can be countered by doubling key sizes.
The Implementation Crisis
Standards exist. Implementation lags dangerously.
A 2023 survey by the Cloud Security Alliance found that only 19% of organizations have begun post-quantum cryptography planning. Fewer than 5% have implemented quantum-resistant algorithms in production environments.
The transition challenges are immense:
-
Hybrid Operations: Organizations must simultaneously support classical and post-quantum algorithms during transition periods, increasing attack surface
-
Performance Overhead: CRYSTALS-Kyber keys are larger than ECDH keys, impacting bandwidth-constrained environments like IoT devices
-
Supply Chain Complexity: Cryptographic libraries, hardware security modules, and third-party services all require updates
-
Legacy Systems: Systems designed without cryptographic agility may require complete replacement
“"The transition to post-quantum cryptography will be the largest and most complex cryptographic migration in history. We are not prepared.”
What This Means for You
The Harvest Now, Decrypt Later threat isn't abstract. It demands immediate action at every level.
For Governments
National security establishments are moving, but slowly. The NSA's Commercial National Security Algorithm Suite 2.0, released in 2022, mandates post-quantum algorithms for all classified systems by 2030. However, intelligence officials privately acknowledge the timeline may be too slow for data already harvested.
For Enterprises
Organizations handling data with 10+ year security requirements face urgent decisions:
- Conduct cryptographic inventories to identify exposed systems
- Prioritize transition for high-value, long-lived data
- Implement cryptographic agility to enable rapid algorithm rotation
- Engage with vendors on post-quantum roadmaps
For Individuals
Personal encryption options remain limited, but emerging tools offer protection:
- Signal has implemented preliminary post-quantum key exchange (CRYSTALS-Kyber)
- Apple announced iMessage post-quantum support in early 2024
- VPN providers are beginning post-quantum integration
Harvest Now, Decrypt Later represents a fundamental shift in how we must think about information security. The assumption that encryption protects data indefinitely is no longer valid. State actors have already exfiltrated encrypted data at scale, betting that quantum computing will render that data readable within the next decade. The transition to post-quantum cryptography is not optional — it is an existential necessity for any organization whose data retains value beyond 2030. The question is not whether you should act, but whether you're already too late.
Sources: National Security Agency Quantum Computing Working Group Assessments (2021-2023); NIST Post-Quantum Cryptography Standardization Project Final Reports; National Academies of Sciences, "Quantum Computing: Progress and Prospects" (2019, updated 2023); Cloud Security Alliance Quantum-Safe Security Working Group Survey (2023); Five Eyes Joint Advisory on Chinese Cyber Operations (2023); Microsoft Digital Defense Report (2023); IBM Quantum Development Roadmap; Michele Mosca, Institute for Quantum Computing, University of Waterloo.
This is a Premium Article
Hylē Media members get unlimited access to all premium content. Sign up free — no credit card required.