Your Hospital's MRI Machine Is Running Windows XP
83% of U.S. hospitals operate medical devices on unpatchable operating systems. The FDA approval process creates a lock-in trap manufacturers exploit.
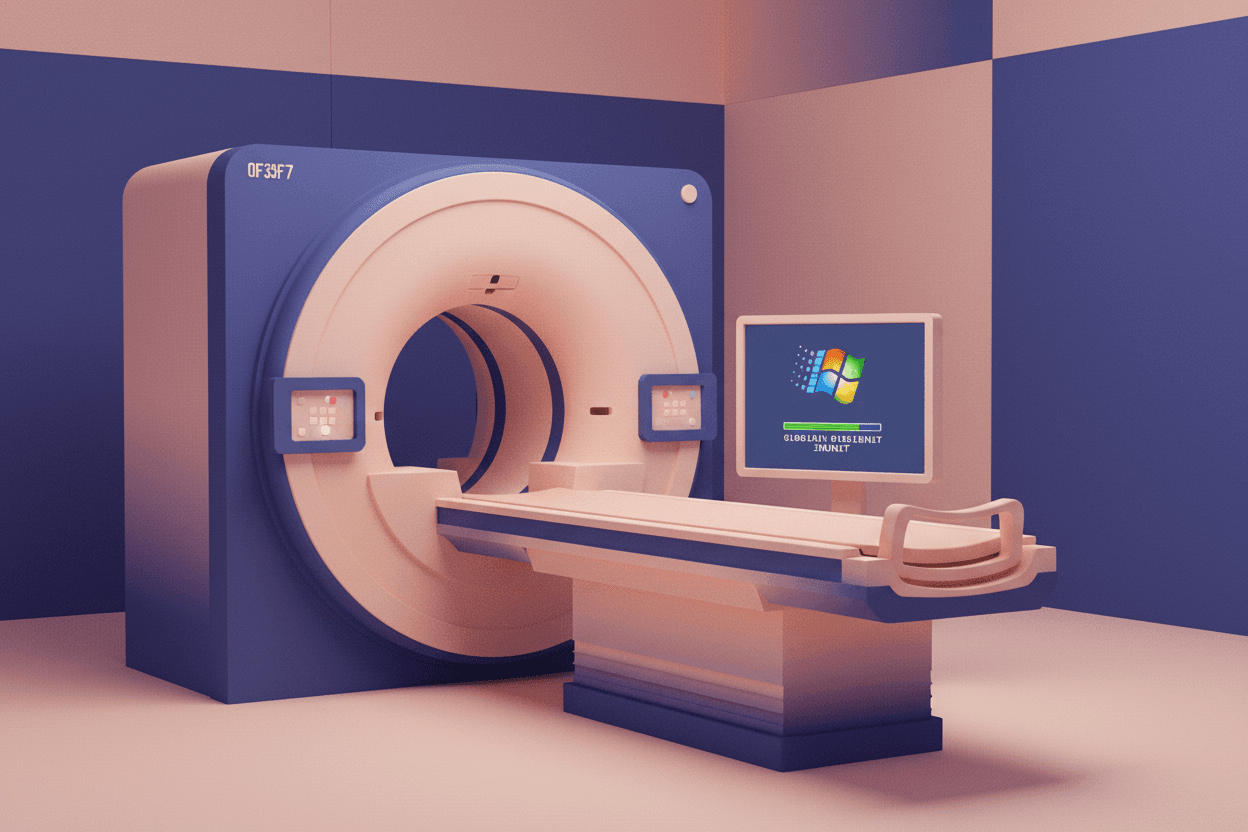
The MRI machine scanning your brain may be running Windows XP. Not because the hospital is cheap — but because updating the software requires FDA re-approval, and the manufacturer stopped paying for that years ago.
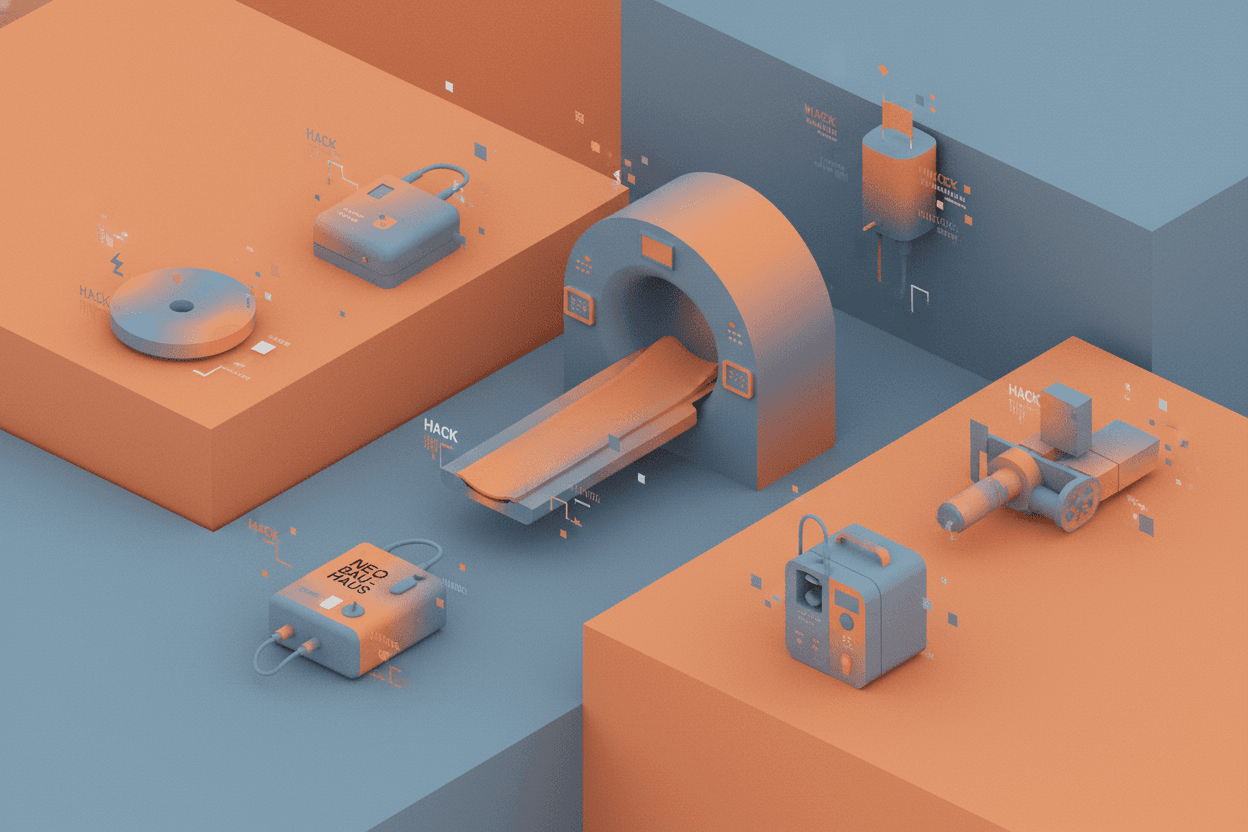
In 2022, Cynerio researchers surveyed over 300 U.S. hospitals and discovered that 83% operate at least one IoT medical device running on an obsolete, unpatchable operating system. These aren't fringe devices in storage closets — they're infusion pumps delivering chemotherapy, MRI scanners diagnosing tumors, and ventilators keeping patients alive in ICUs. The Windows XP embedded in that GE MRI scanner isn't a quirky anachronism. It's a structural vulnerability baked into the regulatory economics of medical device manufacturing.
Here's the question that should keep hospital CISOs awake at night: If a ransomware gang exploits a known Windows vulnerability in your CT scanner, who bears liability when patient care shuts down? The hospital that couldn't update the software? The manufacturer that stopped supporting it? Or the FDA framework that made updates economically irrational?
The FDA Approval Lock-In
The core mechanism trapping medical devices in software amber is the FDA's premarket approval process. When a manufacturer submits a device for 510(k) clearance or Premarket Approval (PMA), the submission includes specific software versions. Any material change — including an operating system upgrade — potentially triggers a new approval cycle.
[!INSIGHT] A single FDA 510(k) submission costs between $5,000 and $250,000 in direct fees, plus $2-5 million in supporting documentation, clinical testing, and regulatory consulting. PMA pathways can exceed $100 million total.
The regulatory logic is sound: software changes can introduce bugs that compromise patient safety. A pacemaker's timing algorithm must behave identically across millions of heartbeats. But this safety guarantee creates a perverse economic incentive structure:
-
Manufacturers face no obligation to support older devices. Once a product line reaches end-of-life, continuing to fund FDA submissions for OS patches becomes a pure cost center.
-
Hospitals cannot legally bypass manufacturers. Modifying FDA-approved software — even to install security patches — violates the Federal Food, Drug, and Cosmetic Act.
-
The approval timeline (6-18 months) exceeds vulnerability lifecycles. By the time a patched version receives clearance, attackers have moved on to newer exploits.
The mathematical expectation for a device manufacturer is straightforward:
$$E[Update] = -C_{FDA} - C_{Engineering} + P(Recall) \times C_{Liability}$$
Where the probability of a recall-causing security incident (P(Recall)) remains low enough that paying for FDA re-approval is almost always negative expected value for devices past their prime revenue years.
The Cynerio Data: A Systemic Failure
The 2022 Cynerio report exposed the scale of this regulatory capture nightmare. Their telemetry analyzed over 10 million connected medical devices across healthcare networks:
| Operating System | Device Share | Security Status |
|---|---|---|
| Windows 10/11 | 17% | Patchable |
| Windows 7 | 31% | End-of-support |
| Windows XP/Embedded | 24% | Unpatchable |
| Linux (various) | 19% | Mixed |
| Proprietary/Other | 9% | Variable |
The implications extend beyond theoretical vulnerability. In 2017, the WannaCry ransomware attack crippled NHS England, forcing hospitals to divert emergency patients. The attack vector? The EternalBlue exploit targeting SMBv1 — a protocol that should have been disabled years prior but remained active on Windows XP-based medical imaging systems.
“"We had MRI machines that couldn't be patched because the manufacturer wouldn't support it, and we couldn't touch it because of FDA rules. We were literally choosing between regulatory compliance and cybersecurity.”
The attack equation for adversaries is equally clear:
$$E[Attack] = P(Vulnerable) \times P(Detection)^{-1} \times Value_{Ransom}$$
When 83% of hospitals present known-vulnerable attack surfaces that cannot be remediated, P(Vulnerable) approaches certainty for targeted campaigns.
The No-Win Scenario for Hospitals
Hospital administrators aren't negligent. They're trapped in a coordination problem with no clean solution.
Option A: Replace devices proactively
- Cost: $1-3 million per MRI scanner, $500,000-$2 million per CT scanner
- Timeline: 12-24 months procurement cycle
- Problem: Capital budgets can't absorb accelerated depreciation
Option B: Network isolation
- Implementation: Air-gap vulnerable devices or VLAN segmentation
- Problem: Modern clinical workflows require DICOM connectivity to PACS servers, EMR integration, and remote specialist access
Option C: Accept risk and insure
- Implementation: Transfer cyber risk to insurance markets
- Problem: Cyber insurance premiums for healthcare increased 100-200% from 2020-2023; many policies now exclude legacy system incidents
The game-theoretic equilibrium is grim: hospitals rationally defer replacement until forced by failure or breach, manufacturers rationally abandon support when revenue declines, and regulators rationally maintain safety standards that incidentally prevent security updates.
“[!NOTE] The FDA's 2023 Cybersecurity in Medical Devices guidance attempts to address this by requiring "reasonable assurances" of post-market security support. However, the guidance applies only to new submissions”
Structural Solutions on the Horizon
Several policy interventions could break this deadlock:
1. Modular Software Approval The FDA could approve software components independently, allowing OS patches without re-validating application-layer code. The FDA's 2019 Pre-Cert program pilots this approach but remains voluntary and limited.
2. Mandatory Support Periods EU MDR regulations now require manufacturers to specify support periods at approval. The U.S. could mandate minimum 10-year security support windows tied to device lifecycle.
3. Safe Harbor for Security Patches Congress could create a limited exemption allowing hospitals to apply OS security patches without violating FDA rules, provided changes are documented and don't alter device functionality.
4. Liability Reallocation Current tort law makes hospitals liable for patient data breaches but shields manufacturers who abandon devices. Extending product liability doctrine to include "foreseeable cybersecurity failure" would realign incentives.
The Biden administration's March 2023 National Cybersecurity Strategy explicitly calls for shifting liability to software vendors — a potential watershed moment if applied to medical device manufacturers.
Sources: Cynerio "State of IoMT Security Report" (2022); FDA "Cybersecurity in Medical Devices: Quality System Considerations and Content of Premarket Submissions" (2023); NHS Digital "Lessons Learned Review: WannaCry" (2018); U.S. National Cybersecurity Strategy (2023); Ponemon Institute "The Cost of Insecure Medical Devices" (2022).